Jeroen van der Ham
One morning two weeks ago, security researcher Jeroen van der Ham was traveling on a train in the Netherlands when his iPhone suddenly displayed a series of pop-up windows, rendering him unable to use the device.
“My phone gets these popups every few minutes and then my phone restarts,” he wrote to Ars in an online interview. “I tried putting it in lockdown mode, but that didn’t help.”
To van der Ham’s surprise and chagrin, the same weak stream of pop-ups on the afternoon commute home again hit not only his iPhone, but the iPhones of other passengers in the same train car. Then, he noticed one of the same passengers nearby as he had that morning. Van der Ham put two and two together and made the passenger appear guilty.
“He was frantically working on some kind of app on his MacBook, had his iPhone out by itself, connected via USB, so he didn’t even notice what was going on even though the Apple devices around him were restarting,” he said. said. “Your phone becomes almost unusable. You can still do things between minutes, so it’s really annoying to experience. Even as a security researcher who hears about this attack, it’s really hard to realize that’s what’s happening.
“The jig is up”
The culprit, it turned out, was using a Flipper Zero device Send Bluetooth pairing requests to all iPhones in radio range. This slim, lightweight device has been available since 2020, but in recent months, it’s become more visible. It acts as a swiss army knife for all types of wireless communications. It can communicate with radio signals including RFID, NFC, Bluetooth, Wi-Fi or standard radio. People can use it to secretly change the channels of a TV in a bar, clone some hotel key cards, read the RFID chip implanted in pets, open and close some garage doors, and prevent the normal use of iPhones.
These types of hacks have been possible for decades, but they require specialized equipment and a fair amount of expertise. The capabilities typically require expensive SDRs – software-defined radios – which, unlike traditional hardware-defined radios, use firmware and processors to digitally recreate radio signal transmissions and receptions. The $200 Flipper Zero isn’t an SDR in its own right, but as a software-controlled radio, it can do a lot more affordably and in a more convenient form factor than previous-generation SDRs.
“The jig is up: software radios have made previously inaccessible attacks available to more people than ever before, and work on them will continue,” Dan Guido, CEO of security firm Trail of Bits, wrote in an interview. “Tech-savvy people can now easily clone most hotel or office keycards. They don’t need any knowledge of signals or messing around with open source code or Linux. [It] Certainly democratizing some previously complex RF [radio frequency] Hacking in the hands of mere mortals.”
The Flipper Zero manufacturer bills the device as a “portable multi-tool for pentesters and geeks” that’s perfect for hacking radio protocols, building access control systems, repairing hardware, cloning electronic key cards and RFID cards, and being used as a universal TV remote. . Its open-source design allows users to flash the device with custom firmware to gain new capabilities.
Some of the specifications for the device are as follows:
- 1.4-inch monochrome LCD display
- GPIO pins for connecting external hardware greatly expand its capabilities
- USB-C port for power and firmware updates
- microSD card slot
- Infrared transceiver
- Sub-1 GHz antenna
- TI CC1101 chip
- 1-wire pogo pin to read contact keys
- 2000 mAh battery
- Low power MCU
- ARM Cortex-M4 32-bit 64 MHz (Application Processor)
- ARM Cortex-M0+ 32-bit 32 MHz (radio processor)
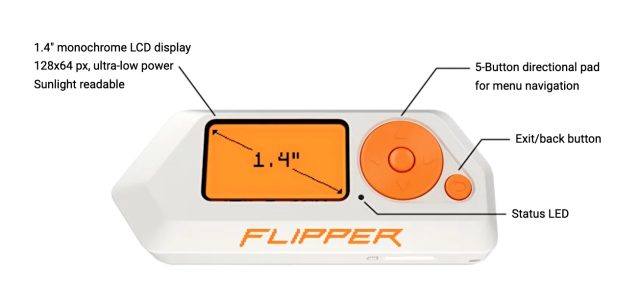
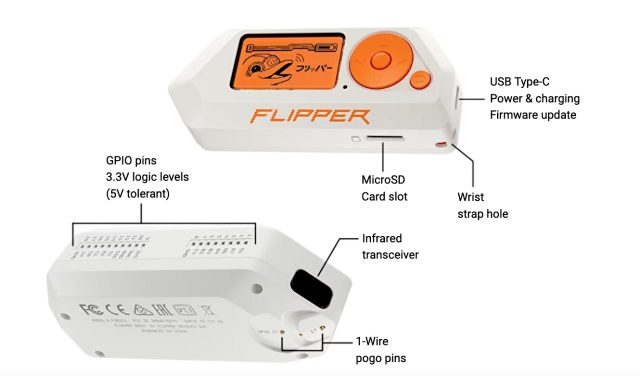
flipperzero.one
“The idea behind Flipper Zero is to connect all the hardware tools needed for research and development on the go,” the manufacturer wrote. “Flipper is inspired by the pwnagotchi project, but unlike other DIY boards, Flipper is designed with the convenience of everyday use in mind – it has a robust case, simple buttons and shape, so no dirty PCBs or scratchy pins.”

